Related Product: SPF Pro (SmartPhone Forensic System Professional)
Editor’s note: Welcome to read our first [Tips] article, we are planning to post this type of article to introduce the small tips of using our forensic tools from time to time. In this post, we are talking about a few things you should keep in mind when you want to make an analysis on smartphone backups.
How to Make Analysis on Smartphone Backups
There are 3 types of source input in SPF Pro, you can load a mobile device, a file or a folder for extraction and analysis. Loading a device is easy to understand, so let’s talk about the other two types.
![[Tips] Mobile Forensics: How to Make Analysis on Smartphone Backups](https://blog.salvationdata.com/wp-content/uploads/2018/12/12.png?w=616)
File Analysis allows you to load and analyze files including iOS/Android backup files, adb backup files, and memory dumps.
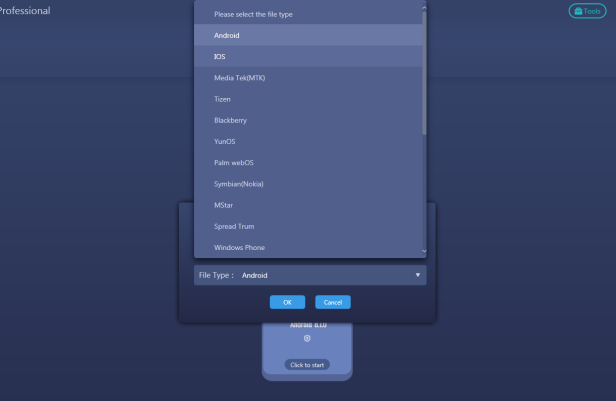
As for Folder Analysis, you can load the iTunes backup folder, Android smartphone backup folder or app data package folder (e.g. com.whatsapp) to perform forensic extractions.
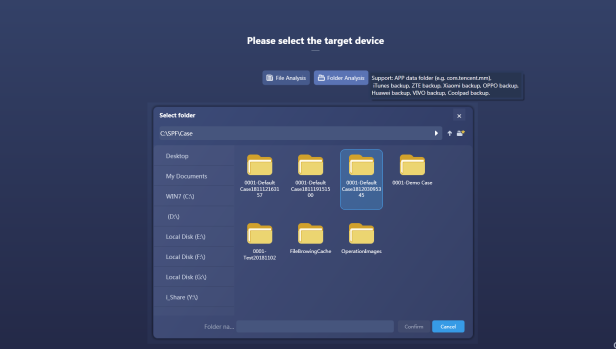
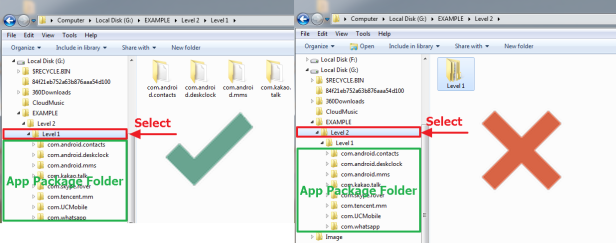
When you are using folder analysis, there are a few things to keep in mind. The folder you specify a source of extraction must directly hold the backup files or app package folders. As below figure shows, when you want to load a number of app package folders for analysis, you must select the level 1 folder that holds these package folders as a forensic source. If you select the level 2 folder with level 1 folder in the middle, SPF Pro is not able to find the app package folder. Therefore, your extraction may fail in the end.
Conclusion
Thanks for reading our first [Tips] article! Keep following our blog, we’ll be posting more helpful small tips in the future. If you are interested in our mobile forensic product, come and check out our website for more information. You can also go to our resource page to download our forensic products for free. We welcome you to contact us and claim your free product trial!
