Editor’s Note: Digital forensic investigation on mobile devices requires investigators to follow step by step workflow to extract and analyze digital evidence. In this article, forensic experts from SalvationDATA will have a technical walkthrough on Android forensic data extraction using ADB to collect crucial device artifacts for digital forensic analysis and investigation.

Forensic Workflow
To perform forensic data extraction from Android devices using ADB commands, first we need to learn the forensic workflow step by step.
To accomplish the complete extraction of digital evidence from Android devices, the primary step is data collection or device extraction. Android forensics depends on the level of access a device provides which further determines the level or depth of the data which investigators can extract. Generally, Android OS provides two layers of user access control which are rooted or non-rooted access. Primarily, Android OS does not provide user administrative or root access hence devices are manufactured with non-root access.
Forensic Investigation requires an in-depth recovery of artifacts for complete analysis. A rooted device provides complete extraction of user data and access to the system partition. The system partition stores complete application data, ROM, and system files. For a non-rooted user, the partitions and system folders are kept hidden with no access.
Data extraction from Android devices in simple words can be defined as the workflow to make a secure copy of the device where we can extract and analyze artifacts to discover crucial evidence. It depends on the following factors for data extraction:
1. Device Security
Android devices come with inbuilt security to prevent users from gaining device access with ease. The following security has to be bypassed or device has to be unlocked in-order to proceed further:
Pattern
1) A pattern-based lock can be set by the user where a custom pattern is required to unlock the device
2) Unlocks the device by using a specific swipe pattern along with a series of nine dots.
3) Pattern locks are stored in gestures.key file which can be replaced to bypass pattern security if the device already has root access and USB debugging is enabled.
Password
1) A lock can be set with 4 to 17 characters which include alphanumeric & mixed case passphrase. This is a highly secure device lock which requires a combination of manual and automated techniques to gain device access
2) Password.key file stores the password set by the device users which is accessible with only root access.
2. Device Unlocking
Fingerprint
Fingerprint-based device unlock can be set for limited devices, it comes as an alternate unlock mechanism set with password/pattern or pin-based locks.
Bluetooth Device Lock & Unlock
A Bluetooth device can be utilized for device smart unlock which is an alternative unlock method set with password/pattern or pin-based locks.
Android Version
1) Android version becomes a crucial factor in gaining device access. It keeps on updating and releasing new versions securing mobile devices. From providing different mechanisms for device locking to enabling full device encryption android has reached a state where gaining physical access becomes cumbersome.
2) From an investigator’s point of view, an unlocking device is a primary step towards extraction. Hence different techniques have to be applied to bypass security based on the version the android is using.

3. Device Accessibility
Non-Root Access
1) Generally manufacturer and Android do not provide root access to the device owner by default. Non-rooted devices provide access to the internal and external memory storage medium which enables an investigator to perform the logical extraction of the device.
2) The system, memory, and internal partitions won’t be visible or accessible. However, full device backup or ADB backup can be utilized to perform logical acquisition of the device.
Root Access
1) A device with complete administrative access is what you get after rooting the device. Access to the device system, memory, and internal partitions are granted to the superuser or the root user.
2) For rooted devices a complete device acquisition can be performed using dd command or automated tools. Root access also allows an investigator to perform data recovery and carving which uncovers deleted evidence stored in the device.

4. Device Connection
Mobile device extraction proficiency depends on the connection medium investigators use to extract a device. The following mediums can be utilized to extract a mobile device which depends on availability and device status:
USB Connectivity
USB cable connectivity is considered to be the safest & proficient method to perform mobile device extraction. For mobile extraction using the USB cable the following settings have to be ensured for uninterrupted device extraction:
1) Connection Mode: MTP
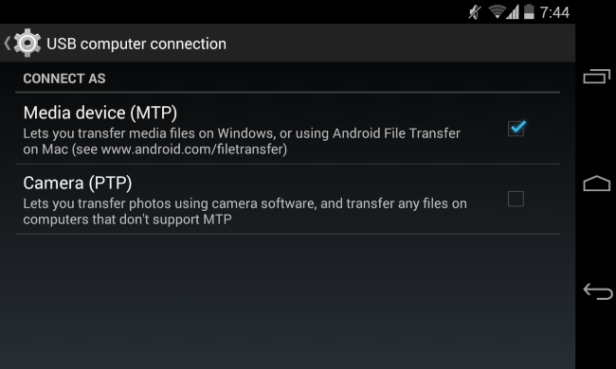
MTP connection mode allows logical access to the device’s internal memory. It is different from the previously used connection medium (USB Mass Storage) which used to emulate the internal memory as a logical partition rather than mounting as a media device.
2) Enabling USB debugging
USB debugging is a developer option which enables analysis machine to establish a connection with the device where SDK functions are enabled. In simple words execution of Linux commands in terminal using ADB can be performed.
Other Connection Mediums:
Device extraction is proficient using the USB cable as the investigator can terminate incoming or outgoing wireless connections by placing the device in flight mode. However, if the USB connection cannot be established then other wireless connection mediums can be utilized:
1) Bluetooth: Mobile extraction can be performed by utilizing ADB via Bluetooth connection.
2) Wireless: Both mobile device and extraction machine has to be connected to the same wifi network. Device extraction can be performed by using an android device bridge via WiFi.
Conclusion
Above is the workflow that we should know before we accomplished the complete extraction of digital evidence from Android devices using ADB (Android Debug Bridge). Thanks for your reading, we will continue to talk about the knowledge of ADB and mobile device extraction procedure, Stay tuned for our next post!
